Is Your Phone Listening? Understanding Microphone Access and Mobile Security
Mission Critical
Your Phone Is Quiet. That Doesn't Mean It's Silent.
Ever chatted with a friend about something private, only to open your phone later and see an ad or push notification about it? It feels like your device is listening, right?
You place your phone on the table during a meeting. It looks harmless. But mobile device security has never mattered more than it does today.
Most people ask, “Is my phone listening?”
Organizations ask a different question:
“Is this device secure enough for our mission?”
That shift in mindset changes everything. Mobile device security is no longer an IT checkbox. It is a business risk. It is a public safety issue.
In some cases, it is a national security matter.
Let's unpack why microphone access is part of a much bigger story.
Why Mobile Device Security Is Now a Board-Level Issue
Data breaches are expensive.
Reputation damage is worse.
Operational disruption can be catastrophic.
According to the IBM Cost of a Data Breach Report, the global average breach cost remains in the millions of dollars. Mobile endpoints are frequently involved.
Meanwhile, research from the Pew Research Center shows that most users worry about how their mobile data is collected and used.
Regulators are also tightening requirements.
Privacy laws evolve every year.
Compliance expectations increase.
Mobile device security now affects:
- Executive leadership
- IT governance teams
- Public safety agencies
- Critical infrastructure operators
It is no longer just about convenience.
It is about control.
How Microphone Access Expands the Attack Surface
When we talk about mobile privacy risks, microphone access often triggers emotion.
But the real issue is architecture.
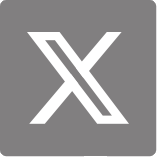
Here is how microphone access typically works:
This flow is not automatically malicious.
But every permission increases exposure.
The National Institute of Standards and Technology emphasizes layered security principles. One defensive layer is never enough.
In consumer smartphones, microphone access control is usually software-based.
If the operating system is compromised, controls can weaken.
That is why mobile device security must be evaluated beyond app settings.
Myth vs. Operational Reality
Let's clarify common beliefs.
|
Popular Belief |
Technical Reality |
Security Impact |
|
Phones always record conversations |
No verified evidence at scale |
Risk depends on permissions and malware |
|
Only celebrities are targeted |
High-value roles are targeted |
Executives and officials face real exposure |
|
Privacy is personal |
In critical roles, privacy is operational |
Operational planning can leak |
For everyday users, risks may be manageable.
For sensitive roles, mobile surveillance can expose mission details.
This is where context matters.
Consumer Smartphone vs. Secure Smartphone
Not all devices are designed for the same purpose.
Here is a simplified comparison:
|
Feature |
Consumer Smartphone |
Secure Smartphone |
|
Microphone access control |
App-level permissions |
Hardware + whitelist enforcement |
|
Encryption key storage |
OS-managed |
Dedicated secure element |
|
App ecosystem |
Open marketplace |
Restricted or validated apps |
|
Tamper detection |
Minimal |
Multi-layer anti-tampering |
|
Security updates |
Vendor cycle |
Often policy-controlled |
A consumer smartphone prioritizes flexibility.
A secure smartphone prioritizes controlled environments.
Neither is “good” or “bad.”
But they serve different risk profiles.
Mobile device security should match the mission, not the trend.
Who Should Be Concerned About Mobile Privacy Risks?
Mobile privacy risks are not evenly distributed.
High-exposure roles include:
- Government agencies handling classified data
- Law enforcement coordinating field operations
- Corporate executives discussing mergers
- Energy sector operators managing grid systems
- Transportation authorities overseeing public networks
In these environments, microphone access control is not about ad targeting.
It is about operational integrity.
If a device is compromised, the consequences extend beyond inconvenience.
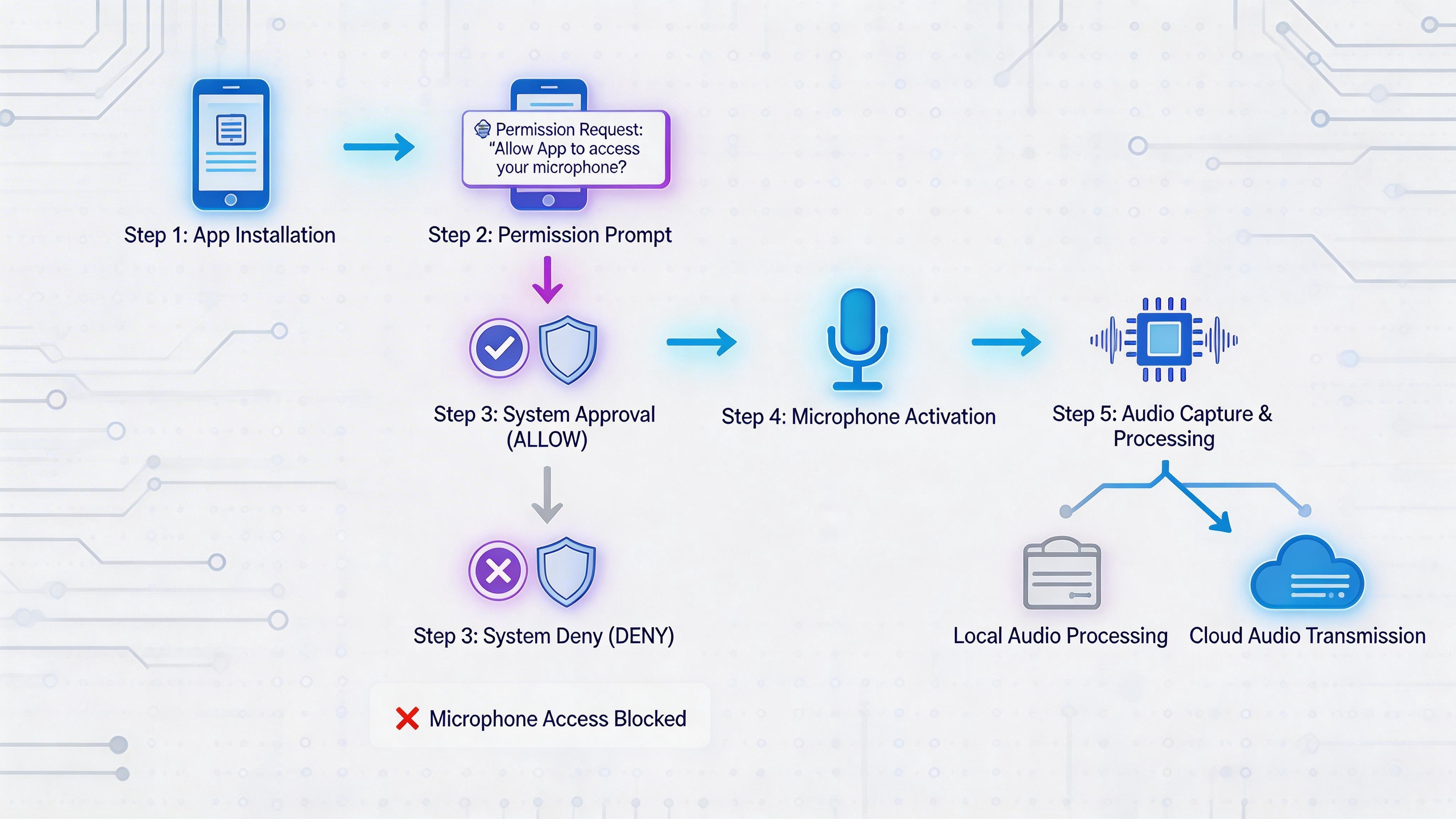
The Four Layers of Modern Mobile Device Security
Strong mobile device security is built in layers.
1. Hardware Root of Trust
This layer verifies the device at power-on.
It ensures firmware has not been altered.
Hardware-based key storage reduces exposure.
2. Secure Boot Chain
Every startup step is validated.
If integrity fails, the device should not boot.
This prevents persistent malware.
3. Application Sandboxing
Apps operate in isolated environments.
They cannot freely access system resources.
Microphone access control becomes enforceable.
4. Policy-Level Device Management
Administrators define usage rules.
Remote lock and wipe functions protect lost devices.
Access policies align with compliance standards.
When these layers align, mobile surveillance risk decreases significantly.
When one layer fails, exposure grows.
Why Open App Ecosystems Increase Complexity
Open app ecosystems drive innovation.
They also increase unpredictability.
Millions of apps exist across marketplaces.
Not all are reviewed equally.
Supply chain vulnerabilities can hide in updates.
Even trusted apps can become compromised.
Even small code changes can introduce risk.
Mobile device security in open ecosystems depends heavily on patch speed and user behavior.
In high-risk sectors, this model may not be sufficient.
That is why some organizations adopt purpose-built secure smartphone platforms with restricted app environments.
Practical Checklist for Organizations
Before deploying smartphones in sensitive environments, ask these questions:
Device Integrity
- Does the device support hardware-rooted security?
- Are encryption keys stored in a secure element?
- Is secure boot enforced at startup?
Microphone Access Control
- Can microphone access be restricted by whitelist?
- Can permissions be centrally managed?
- Are hardware-level controls available?
Mobile Privacy Risks
- Is location tracking configurable?
- Can wireless interfaces be disabled by policy?
- Is metadata logging monitored?
Incident Response
- Is remote wipe immediate?
- Can compromised devices be isolated?
- Are logs auditable?
This checklist transforms fear into evaluation.
Mobile device security becomes measurable.
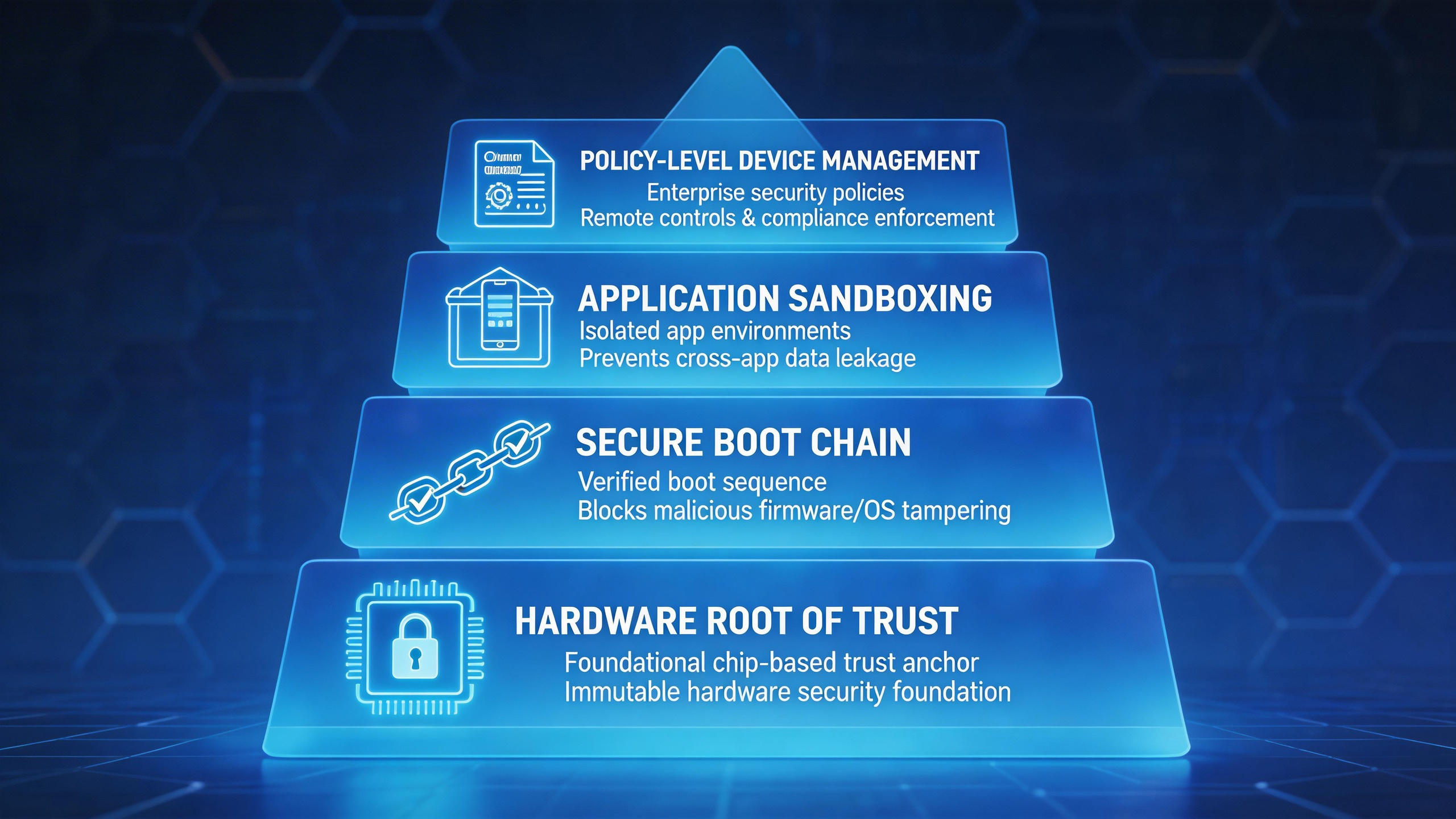
Mobile Surveillance: The Broader Context
Microphone access is only one component.
Mobile surveillance can also involve:
- Location tracking
- Network interception
- Metadata aggregation
- Bluetooth probing
When these signals combine, patterns emerge.
Patterns reveal behavior.
Behavior reveals operational routines.
In public safety scenarios, this can expose patrol schedules.
In corporate settings, it can reveal negotiation timelines.
Mobile privacy risks rarely appear dramatic.
They accumulate quietly.
Why the Conversation Is Growing
Search interest in mobile privacy continues to rise.
Organizations are reassessing device policies.
Procurement teams ask tougher questions.
Cybersecurity incidents make headlines weekly.
Mobile endpoints are part of the ecosystem.
Mobile device security now intersects with:
- Data protection regulations
- Critical infrastructure resilience
- National cybersecurity strategies
The discussion is maturing.
It is moving from paranoia to policy.
Internal Security Culture Matters
Technology alone cannot solve mobile privacy risks.
User training matters.
Clear policies matter.
Role-based access control matters.
Employees should understand:
- Why certain apps are restricted
- Why microphone access control exists
- Why secure smartphones may replace consumer models in some roles
Security culture reduces resistance.
It builds trust across teams.
Final Thought: Control Defines Trust
So, is your phone listening?
The better question is this:
Is your organization in control of its devices?
Mobile device security is not about suspicion.
It is about architecture.
Microphone access control is not about fear.
It is about governance.
Mobile privacy risks will continue to evolve.
Mobile surveillance capabilities will grow more sophisticated.
But organizations that design for security from the foundation upward gain something critical.
Confidence.
Confidence that conversations remain private.
Confidence that missions remain protected.
Confidence that technology serves the organization — not the other way around.
Mobile device security is no longer optional.
It is strategic infrastructure.
And the quiet device on the table?
It deserves more scrutiny than we once thought.